Share this
Guide to Cloud Computing Advantages and Disadvantages
by Mark Mutch on Apr 1, 2015

"Cloud computing" is the current information technology phrase du jour… The challenge is that everyone has a different definition. As a metaphor for the Internet, "the cloud" is a familiar cliché, but when combined with "computing," or “hosting,” or “data sharing,” or “application,” the meaning gets more complex and less clear.
Wikipedia states:
“The popularity of the term can be attributed to its use in marketing to sell hosted services in the sense of application service provisioning that run client server software on a remote location.”
In a recent study, Luth Research and Vanson Bourne (CA Technologies - NASDAQ: CA) surveyed companies that are currently using cloud services to get specifics on how cloud computing is being used, top problems or successes, and how its use changes as IT teams gain more experience.
Results were revealing — the benefits of using cloud computing are, by all accounts, living up to the hype, and many of the predicted problems are not actually being reported:
- Nearly 100% overall satisfaction with cloud results (innovation, cost, revenue, performance)
- The longer a company used cloud, the more likely that cloud exceeded expectations (71% who have been in the cloud for 4+ years said it exceeded expectations)
- Around 50% of respondents have already moved mission-critical apps to the cloud
- 98% of respondents reported that the cloud met or exceeded their expectations for security.
Definitions You Need to know before moving on
- SaaS - Software as a Service - Delivers a single application through the browser to thousands of customers using a multi-tenant architecture.
- IaaS/PaaS - Infrastructure/Platform as a Service - Also called "cloud hosting" and "utility computing," infrastructure as a service (IaaS) provides the servers and operating systems, while platform as a service (PaaS) adds the databases, runtime engines and other necessary system software for the customer and IT departments to access on demand and run their own applications.
- Web services in the cloud - Web service providers offer APIs that enable developers to exploit functionality over the Internet, rather than delivering full-blown applications.
- Virtualization - Server virtualization allows application workloads to be easily added and removed as self-contained modules.
- Public Cloud – An environment where the services are rendered over a network that is open for public use and accessed only via Internet (direct connectivity is not offered).
- Private Cloud - Provides the same flexibility and self-service capabilities as a public cloud service, but with complete control of privacy. Private cloud is cloud infrastructure operated solely for a single organization, whether managed internally or by a third-party and hosted internally or externally.
- Hybrid Cloud - Contains both private and public components, typically from multiple providers.
All the definitions and success stories aside, what you, the business owner, care about is: “What does it do for me?”
The Purpose of Cloud Computing
Before you can even address the question "to cloud or not to cloud" or weigh cloud computing advantages and disadvantages, you need to make sure you have a clear definition of what your software needs to do: Not only the user and data functions, but important attributes about the software as a business system.

Access - Which users, clients, agencies and staff need access to your software's functions and the data it manipulates? Where are these individuals located and what access to networks is available to them?
Availability - When is access required, time of day, weekends, etc? How critical is access to the system and how long can it be unavailable to users?
Budget - Are there budgetary constraints or timing issues that would impact a possible solution?
Backup and Recovery - If the system goes down, how fast does it need to become available again? How often does data change and how much data is there?
Data sharing - Are there other data/software systems that must share information with this software? Is that sharing real-time or batched? Automated or manual?
Security - How sensitive is the data to your company? Would it be the target of overt action by others to acquire or disrupt? Are there legal or other requirements for security of the data and software interface?
Advantages of Cloud computing
Finally, we can begin weighing in on cloud computing advantages and disadvantages. So, let's get started with the former. Cloud computing can completely change the way companies use technology to service customers, partners and suppliers, giving them new ability and agility.
Cost Efficiency
A big advantage of cloud computing is the elimination of the investment in stand-alone software or servers. By leveraging the cloud’s capabilities, companies can save on licensing fees and, at the same time, eliminate overhead charges, such as the cost of data storage, software updates, management, etc. With the cloud, it is possible to set up one-time-payments or pay-as-you-go to help save on costs that can add up when using a traditional desktop model. A public-cloud delivery model converts capital expenditure to operational expenditure. Here is a better look at some of the areas where cloud computing can save money:
- Servers: There is no longer a need for on-site servers with cloud computing. When using the cloud, you are renting a virtual server instead of a physical one. Your data is stored in a virtual space that can even be paid for by the hour, meaning you can pay for the space only when you need it.
- Employees: The cloud eliminates, or at least reduces the need for an in-house IT staff. Using the cloud allows you to do away with manual updates. Instead of doling out work to a system administrator, who then manually completes the task and makes the resource available, cloud computing uses resource APIs and an orchestration engine to drive the same task. This is the genius of cloud computing.
- Maintenance and Downtime: Cloud outages do happen, sure, but as cloud technology matures, outages have become less common. Cloud providers are able to actively monitor, maintain and upgrade your hosting servers so you don't have to. The decrease in downtime means that you are not held back from business productivity.
Location Independence and continuous availability
Public clouds offer services that are available wherever the end user might be located. There are no longer physical limitations related to server location and storage. The shackles are off. Data storage, computing and networking can all be done in an independent location. This approach enables easy access to information and accommodates the needs of users in different time zones and geographic locations. Traditionally, on-site servers create an island of infrastructure. Infrastructure that exists at data centers, in remote offices, at home, in billions of mobile devices, and in the private cloud. Trying to manage all of these islands is a full time job.
A major benefit of the cloud is readily-available information, resulting in collaboration booms, since it is now easier than ever to access, view and modify shared documents and files.
Backup and Recovery
The process of backing up and recovering data is simplified, since data now resides on the cloud and not on a physical device. The various cloud providers offer reliable and flexible backup/recovery solutions. In some cases, the cloud itself is used solely as a backup repository of the data located in local computers. A few of the benefits of data backup in the cloud are listed below as seen by Staples. Yes, Staples has a blog.
- Redundant Backups: Your data is always stored off-site and is redundantly copied to other servers in different locations. If one goes down, your data can be retrieved from elsewhere on the backup network.
- Security: Data is encrypted by the backup service’s software program on your computer before it is sent to the cloud, so thieves on the Internet can’t intercept it.
- Virus Protection: The backup service software detects any virus or infection before data is sent. If a virus is found, that file is flagged and not copied to the backup service. You will be notified that the corrupted file has not been deleted from your computer, so you won’t lose any data, but it won’t be backed up online.
In terms of recovery, the entire server, including the operating system, applications, patches and data is compiled into a virtual server. The entire virtual server can be copied, or backed up, to an offsite data center and spun up on a virtual host in a matter of minutes.
As noted by Online Tech, an IT company with data centers offering enterprise hosting, since the virtual server is hardware independent, the operating system, applications, patches and data can be safely and accurately transferred from one data center to a second data center without the burden of reloading each component of the server. This can dramatically reduce recovery times compared to conventional (non-virtualized) disaster recovery approaches where servers need to be loaded with the OS and application software and patched to the last configuration used in production before the data can be restored.
Resiliency and Redundancy
What is cloud resiliency you ask? Well, here is the best definition out there from What is Cloud?:
"Resilient computing is a form of failover that distributes redundant implementations of IT resources across physical locations. IT resources can be pre-configured so that if one becomes deficient, processing is automatically handed over to another redundant IT resource. Within cloud computing, the characteristic of Resiliency can refer to redundant IT resources within the same cloud (but in different physical locations) or across multiple clouds. Cloud consumers can increase the reliability and availability of their applications by leveraging the resiliency of cloud-based IT resources."
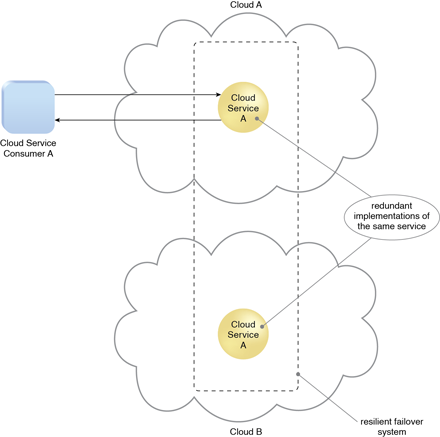
Put more simply, cloud resiliency is the ability of a data center and its components — servers, storage, etc. — to continue operating in the wake of some kind of disruption, whether it's a breakdown of equipment, a power outage or even a natural disaster. A cloud deployment strategy is usually built on a robust architecture, thus providing resiliency and redundancy to its users. The cloud offers automatic failover between hardware platforms out of the box, while disaster recovery services are also often included.
When determining how important cloud resiliency is to your business, there are two major factors that you will want to consider:
- Recovery time objective (RTO): The duration of time and the service level within which a system must be restored after a disruption to avoid a break in business continuity. It refers to the point in time when complete business operations have resumed.
- Recovery point objective (RPO): The maximum tolerable period in which data might be lost. Focused on backup frequency, it refers to the point in time in the past to which a system is recovered.
Scalability with your business needs
A key feature of cloud computing is scalability. You are able to upscale or downscale your operations on the cloud with ease as your IT requirements change. What does this mean for your business? Well, because cloud computing is so scalable, many organizations are relying on managed data centers where a trained cloud technician can maintain and scale shared, private and hybrid clouds.
The idea of utilizing a data center isn't just an option for enterprise companies, either. Even a small business can find value in using data centers to help manage their cloud computing. Cloud computing allows for quick and easy allocation of resources in a monitored environment where overloading is never a concern, as long as the system is managed properly.
Storage to help you Manage your data
The cloud can accommodate and store much more data, compared to a personal computer and, in a way, offers almost unlimited storage capacity. It eliminates worries about running out of storage space and at the same time, it spares businesses the need to upgrade their computer hardware, further reducing the overall IT cost. Cloud computing information storage is driven primarily by these five factors, according to IDC.
- Enabling efficient delivery of information
- Reducing information infrastructure deployment costs
- Minimizing costs associated with unpredictable information workloads
- Lowering the costs of long-term information archive
- Simplifying real-time analysis of information (big data).
Storage needs will vary vastly from business to business and there are storage options for everyone. Some storage platforms offer a limited amount of data for a cheap price and get progressively more expensive as they scale up. Others start off at a more expensive rate, but offer bigger storage plans at a lower rate. The price will obviously vary based on your business needs, but for 1TB of storage, the cost can vary from as little as $250 up to thousands of dollars per year.
If you're serious about finding a cloud provider that best suits your storage needs, check out the best Business Cloud Storage Services.
The Convenience of Device Independence
Cloud computing services can be accessed via a plethora of electronic devices that are able to have access to the internet. Cloud computing is device-independent because cloud-based resources can be accessed from any computer on the Internet, but also any type of computer. This means that any device with an internet connection and a web browser is capable of access. These devices include not only the traditional PCs, but also smartphones, tablets, etc.
What makes device independence a valuable feature is that it allows for users to move from their desktops at work to virtually any location and work from anywhere. Home computers, laptops, netbooks, smartphones, and tablets can reach the same information that their work desktop can access, ensuring that they will always have access to the latest version of their files.
Disadvantages of Cloud Computing
Cloud computing is certainly not a cure-all for business; Cloud computing still has issues with certain application needs that need to be specifically addressed. The Cloud Security Alliance (CSA) has put together a list of the nine most prevalent and serious security threats in cloud computing, known as the "Notorious Nine: Cloud Computing Threats in 2013." Listed below is an outline of these nine security threats that come with cloud computing and encompass the primary disadvantage of cloud computing.
Data Breaches
In the Notorious Nine report, the CSA notes, "It's every CIO's worst nightmare: the organization's sensitive internal data falls into the hands of their competitors." Cloud computing has introduced new avenues for cyber attacks and putting data at risk. Of course, there are ways to prevent data loss and strengthen data security, but it's a double edged sword. Encryption protects data at rest, but lose the encryption key and you've lost the data. The cloud routinely makes copies of data to prevent its loss due to an unexpected die-off of a server. The more copies, the more exposure you have to breaches.
Data Loss
The prospect of seeing your valuable data disappear into the ether without a trace can leave you skeptical to use cloud services. The data loss can happen in a variety of ways: It can occur when the owner of encrypted data loses the key that unlocks it; A malicious hacker might delete a target's data out of spite; or, you could lose your data to a careless cloud service provider or a disaster, such as a fire, flood or earthquake.
Small amounts of data were lost for some Amazon Web Service customers as its EC2 cloud suffered "a remirroring storm" due to human operator error on Easter weekend in 2011. The risks of data loss present many challenges for businesses considering cloud service. Compounding the challenge, encrypting your data to ward off theft can backfire if you lose your encryption key.
Account or Service Traffic Hijacking
Should a hacker gain access to your credentials, they will be able to monitor your activities and transactions, manipulate data, and redirect clients incorrectly. "Your account or services instances may become a new base for the attacker. From here, they may leverage the power of your reputation to launch subsequent attacks." (CSA report)
Insecure interfaces and APIs
IT administrators rely on interfaces for cloud provisioning, management, orchestration and monitoring. APIs are integral to security and availability of general cloud services. From there, organizations and third parties are known to build on these interfaces, injecting add-on services. "This introduces the complexity of the new layered API; it also increases risk, as organizations may be required to relinquish their credentials to third parties in order to enable their agency," the CSA report notes.
Denial of service
DoS has been an Internet threat for years, but it becomes more problematic in the age of cloud computing when organizations are dependent on the 24/7 availability of one or more services. DoS outages can cost service providers their customers and prove to be pricey to customers who are billed based on compute cycles and disk space consumed.
Malicious insiders
Any number of supposed allies can gain access to a network, system or data for malicious purposes — from a current or former employee, a contractor, or a business partner who wishes to do harm to data. In an improperly designed cloud scenario, a malicious insider can wreak even greater havoc. In situations where a cloud service provider is solely responsible for security, the risk is great. "Even if encryption is implemented, if the keys are not kept with the customer and are only available at data-usage time, the system is still vulnerable to malicious insider attack," according to CSA.
Cloud abuse
"It might take an attacker years to crack an encryption key using his own limited hardware. But using an array of cloud servers, he might be able to crack it in minutes," the report noted. Another example might be a malicious hacker using cloud servers to launch a DoS attack, propagate malware or share pirated software. The issue is that responsibility for use of cloud services rests with service providers. Therefore, they must be the ones to constitute what is cloud abuse and what isn't, as well as developing best practices in preventing it.
Insufficient due diligence
Organizations that embrace the cloud without fully understanding the cloud environment are at a substantially higher risk than those who do have an understanding. "Too many enterprises jump into the cloud without understanding the full scope of the undertaking," said the report. The CSA's basic advice is for organizations to make sure they have sufficient resources and to perform extensive due diligence before jumping into the cloud.
So, if you don't have extensive knowledge about contractual issues with providers over liability and transparency or operational and architectural issues, then you may be better suited to hire an external IT company to help you out.
Shared Technology
Cloud service providers share infrastructure, platforms and applications to deliver their services in a scalable way. So, one of cloud computing's biggest assets can, in turn, become a liability. "Whether it's the underlying components that make up this infrastructure (e.g. CPU caches, GPUs, etc.) that were not designed to offer strong isolation properties for a multi-tenant architecture (IaaS), re-deployable platforms (PaaS), or multi-customer applications (SaaS), the threat of shared vulnerabilities exists in all delivery models," according to the CSA report.
For a complete look at the "Notorious Nine: Cloud Computing Threats in 2013", check out "9 top threats to cloud computing security," that was originally published at InfoWorld.com.
How to Decide if Cloud Computing is right for you
Because most of the pros and cons (along with your company’s individual situation) are not strictly quantifiable, making a decision about cloud computing can seem somewhat arbitrary. However, a simple Pareto Analysis can help steer you in the right direction (or at least make you feel good about your decision).
Pareto Analysis uses the Pareto Principle – also known as the "80/20 Rule." This is the idea that 20 percent of causes generate 80 percent of results. With this tool, we're trying to find the 20 percent of work that will generate 80 percent of the results that doing all of the work would deliver.
How to Do the Analysis:
Step 1: Identify and List Pros and Cons - First, write a list of the major factors that weight into the decision.
Step 2: Identify the Root Impact of Each - For each factor, identify its fundamental impact.
Step 3: Score Impacts - The scoring method you use depends on the sort of problem you're trying to solve. For example, if you are trying to save time – you could score on a scale of 1 – 10, based on the time-saving of the impact.
Step 4: Group Problems Together By Root Cause - Next, group factors together by impact.
Step 5: Add up the Scores for Each Group
Keep in mind that low scoring factors may not even be worth bothering with — solving these problems may cost you more than the solutions are worth. Want these helpful tips in the form of an eBook? Check out Mark's "Everything You Need to Know About Cloud Computing" eBook.
Photo Credit: Computing Scale
Share this
- May 2026 (3)
- April 2026 (25)
- March 2026 (43)
- February 2026 (20)
- January 2026 (20)
- December 2025 (1)
- November 2025 (1)
- September 2025 (34)
- August 2025 (7)
- July 2025 (1)
- June 2025 (2)
- May 2025 (2)
- April 2025 (3)
- March 2025 (2)
- February 2025 (1)
- January 2025 (1)
- December 2024 (3)
- August 2024 (1)
- July 2024 (2)
- June 2024 (17)
- November 2022 (1)
- February 2022 (1)
- July 2021 (1)
- June 2021 (1)
- May 2019 (1)
- March 2019 (1)
- February 2019 (1)
- October 2018 (1)
- September 2018 (1)
- April 2018 (1)
- March 2017 (1)
- December 2016 (2)
- September 2016 (2)
- January 2016 (1)
- April 2015 (2)
- March 2015 (2)
- February 2015 (1)
- January 2015 (1)
- December 2014 (1)
- September 2014 (1)
- April 2014 (1)
No Comments Yet
Let us know what you think